Overview

As schools grapple with the increasing importance of supporting student mental health and ensuring school safety, all while balancing remote instruction during the Covid-19 pandemic, many are turning to student monitoring technologies to meet these goals. In a recent research survey, 81% of K-12 teachers reported that their schools use monitoring software. As schools shifted to greater virtual engagement with their students during the pandemic, they have increasingly sought tools to protect students when they are online. For example, during the pandemic, 12 more of the 25 largest school districts in the country started using monitoring technology for suicide prevention.
Additionally, the shift to online learning during the pandemic was accompanied by a 28% increase in the number of school-managed devices used by students along with thousands of school-managed Wi-Fi internet hotspots. This increased technology use led to more monitoring of student online activity.
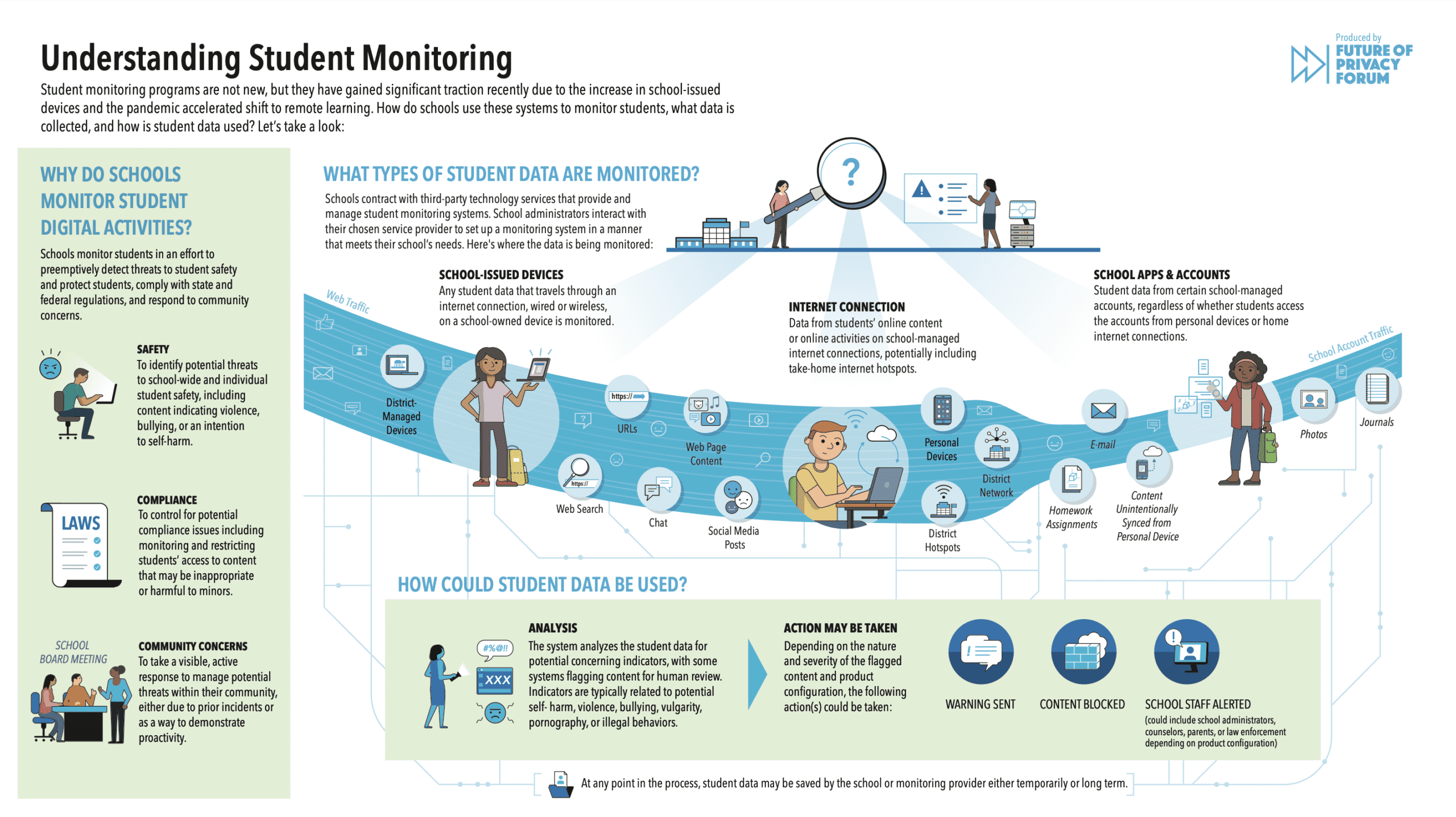
Given the rapid expansion of these tools in schools across the nation, it is important for education leaders, students, and families to understand their use. In a recently published report, FPF examined the unique privacy risks and harms students may experience when schools adopt self-harm monitoring systems without careful guardrails. But what exactly is a student monitoring system, how do schools implement them, and what student information do these systems hold and process? Today, the Future of Privacy Forum released a new infographic, Understanding Student Monitoring, that answers these questions and demystifies how student monitoring works.
FPF’s Understanding Student Monitoring infographic clarifies:
- Why schools may choose to adopt a monitoring system;
- What student information and activities a monitoring service can access;
- How a school and monitoring provider may process and use student information collected through a system;
- What actions may be taken as a result of a monitoring system flagging a student’s activity or information.
The following sections further detail how monitoring works as presented in our new infographic.
Why Do Schools Monitor Students’ Digital Activities?
Schools monitor students in an effort to preemptively detect threats to student safety
and protect students, comply with state and federal regulations, and respond to community concerns.
Safety
To identify potential threats to school-wide and individual student safety, including content indicating violence, bullying, or an intention to self-harm.
 Compliance
Compliance
To control for potential compliance issues including monitoring and restricting students’ access to content that may be inappropriate or harmful to minors. For example, the Children’s Internet Protection Act (CIPA), a federal law, requires the 95% of schools that receive e-rate funding to perform some monitoring to limit students’ exposure to inappropriate, obscene, or harmful content online.
 Community Concerns
Community Concerns
To take a visible, active response to manage potential threats within their community, either due to prior incidents or as a way to demonstrate proactivity.
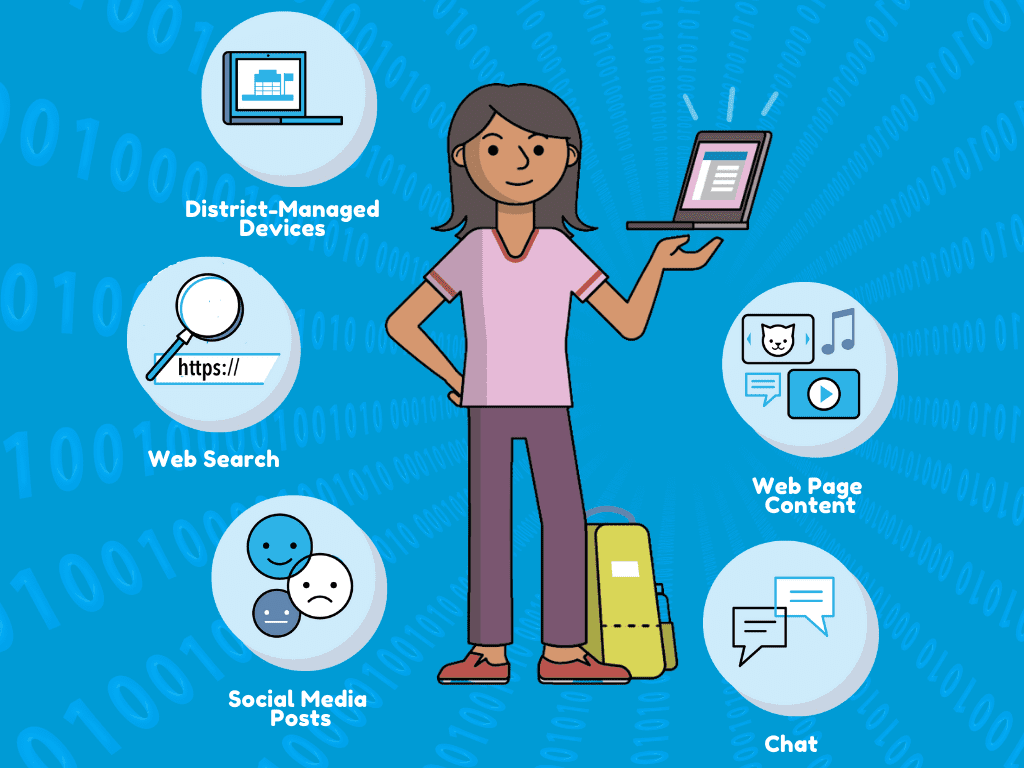
What types of student data are monitored?
Schools implement student monitoring by contracting with a third-party technology service that provides a monitoring system according to the needs and preferences of the school. School administrators may choose from a number of privately available monitoring providers, whose specific systems may use differing indicators and protocols to scan students’ online activities and content. School administrators may be able to configure some of the monitoring system’s settings to increase student privacy or adjust the indicators used.
Regardless of the specific provider’s configurations, any student data that travels through school-managed devices, school-managed internet connections, including Wi-Fi hotspots, or certain school-managed accounts, could be subject to monitoring through the system. As the boundaries of physical school campuses increasingly blur with the virtual learning environment in students’ homes, debate continues about where and when it is appropriate for schools to monitor students.
In general, however, schools often monitor three key categories of student activity. Each of these types of student activity involves at least one technology that is issued to the student and managed by the school, allowing the monitoring system to thereby access student information.
School-Issued Devices
Any device that the school issues to a student, such as laptops or tablets, may be monitored. The monitoring system may access and process any online data from these devices, potentially including students’ online activities when they use these devices at home.
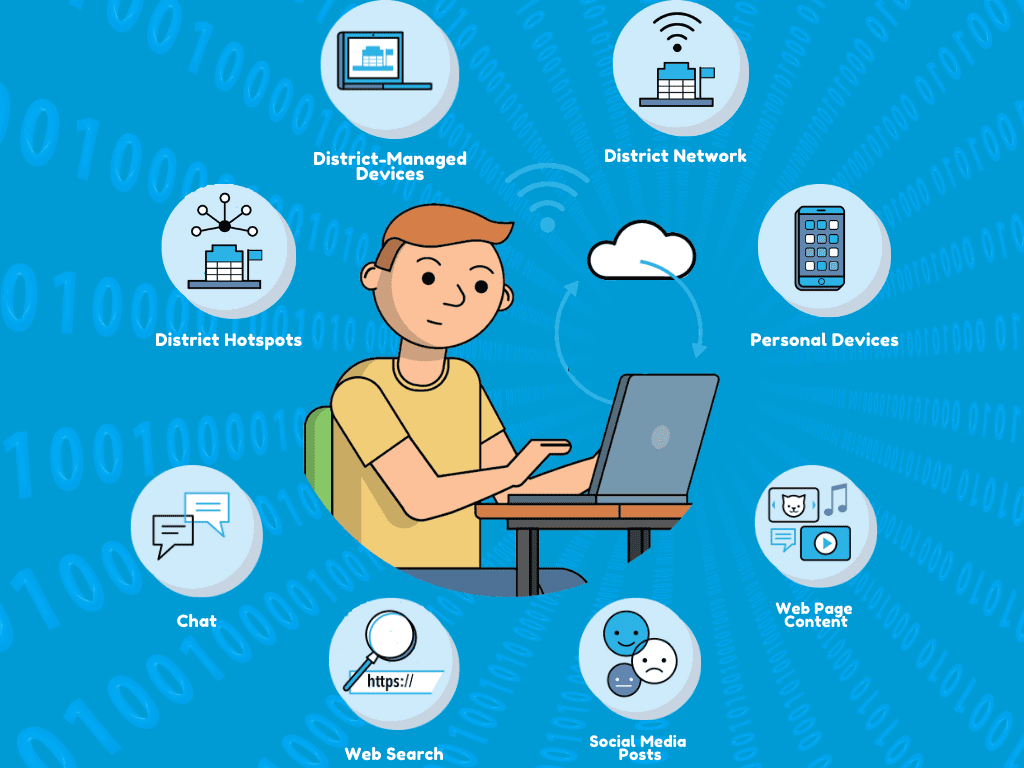
School-Managed Internet Connections
Any online data from any school-managed internet connection may be monitored, including students’ online activities using a take-home Wi-Fi internet hotspot. Students who use personal devices may nonetheless have their online activities subject to monitoring if they connect to a school-managed network, whether at school or at home.
School-Managed Apps and Accounts
Certain student accounts that are managed by the school may be monitored (e.g. Microsoft 365 or Google Workspace), regardless of the internet connection or device that a student uses to access the accounts. For example, depending on the school-managed account and the capabilities of the monitoring system, students who access their school-managed email accounts, videoconferencing or chat applications, or document storage accounts, from a personal device using a non-school
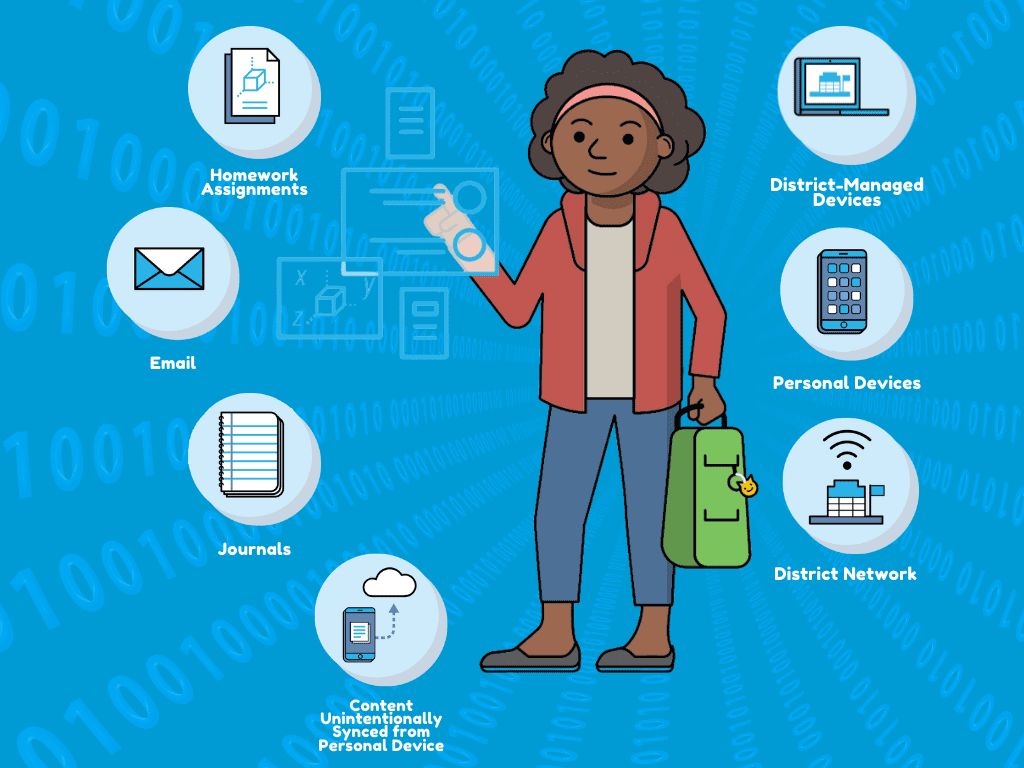
internet connection at home may have their activities monitored. This is because the monitoring occurs at the level of the school-managed app, not at the level of the device or internet connection.
How could student data be used?
Student data collected through school-managed devices, internet connections, or accounts is processed by a monitoring program’s automated system that searches for concerning indicators. These indicators include keywords associated with self-harm, suicide, violence, bullying, pornography, profanity, or illegal behavior. Depending on the nature of a detected indicator, the monitoring provider and school administrators may pursue one or a combination of three follow-up actions to intervene with the student:
Send a Warning
The goal of this action is to inform the student that their activity was deemed concerning and was flagged by the monitoring system. Warnings may often be sent in conjunction with blocking the content in order to prevent the student from accessing potentially harmful material. Warnings may occur live while a student is trying to access sites that the system prohibits, or may occur retroactively as a result of the monitoring system processing student information and detecting indicators in student-generated content.

Block Content
The goal of this action is to protect the student from accessing potentially harmful content online, or to discourage the student from attempting to engage in similar online activities going forward. Monitoring systems often block content in tandem with issuing a warning to the student.
Send an Alert
In cases where the monitoring system may detect student information that may indicate violence or harm to the student or others, the system may generate an alert to inform various adults of the student’s activities. In some cases, if the automated system flags a student’s information or activity, personnel from the monitoring service may provide a human review of the flagged content to determine whether it indicates a true concern and merits alerting other parties. These adults may include school administrators, school IT, parents, and in some cases, law enforcement. The goal of these alerts is to bring the concerning activity to the attention of relevant adults who may be able to further evaluate the validity of the detected concern, intervene, or follow-up with the student. This type of action is distinct from a warning sent to the student, as the monitoring system normally sends an alert to other individuals in response to student activity that it considers to represent a greater level of concern.

Responsible adults who receive the monitoring system’s alert about a student may be able to view the specific activity or content that the system flagged, and in some cases can view additional information about the student’s activity that the system may store. Some monitoring systems may, depending on the school’s configuration, also keep a log of a student’s web browsing activities, including activities that do not contain concerning indicators, that school staff may reference in the event of an alert.
Even when a monitoring system generates an alert to school staff, it may not be accurate. Monitoring systems sometimes incorrectly flag students and draw false conclusions using an automated algorithm. As a result, human reviewers and school staff may find that many students who are detected by the system do not need intervention and their online activities may be developmentally normal and safe. For more on the accuracy of student monitoring systems and the implications of false flags for self-harm, see FPF’s recent report.
The student data collected by the monitoring system may be stored by the monitoring service provider on behalf of the school, depending on the specific system configuration, contract terms, and school policies. Students and families may refer to their school’s data retention protocols and data deletion schedules to learn how long student information collected through any monitoring system is retained. Finally, student data collected through monitoring may be protected by FERPA, as explained further in the Legal Implications section of our recent report.
Additional Resources
FPF Resources:
- The Privacy and Equity Implications of Using Self-Harm Monitoring Technologies
This report describes self-harm monitoring technology and how schools use it, details the privacy and equity concerns introduced by these monitoring systems, points out challenges that undermine the accuracy and limit the usefulness of these systems for addressing student mental health crises, outlines legal considerations related to monitoring students for self-harm, provides crucial questions that school and district leaders should consider regarding monitoring technologies, and offers recommendations and resources to help schools and districts protect students’ privacy in the context of monitoring for self-harm. - School Safety & Privacy: An Animated Introduction
This short video explores some technologies that schools use or are considering, privacy harms that can result from surveillance, and basic steps to help districts safeguard students’ privacy. - A Closer Look: Network Monitoring. This brief covers the issue of network monitoring in schools, supplemented by both FPF and external resources.
- Reopening Schools Issue Brief: Online Monitoring & COVID-19. This brief covers the issues surrounding online monitoring during the COVID-19 pandemic
- Principles for School Safety, Privacy, and Equity
Written by 40 education, privacy, disability rights, and civil rights organizations, these principals are designed to protect students’ privacy, dignity, and right to an equal education - Surveillance Won’t Save Our Kids, Humane Public Policy Can. This blog outlines arguments against surveillance in schools, followed by alternative policy approaches.
- School Safety Measures Must Have Evidence, Be Specific, & Have Privacy and Equity Guardrails. This brief discusses the balance between managing school safety and student privacy in schools in a way that minimizes student harm.
- The Student Privacy Communications Toolkit.
This provides resources for school districts developing their student privacy approach.
Additional Resources:
- Under Digital Surveillance: How American Schools Spy on Millions of Kids. This piece by The Guardian unpacks the prevalence of surveillance in schools and how this could negatively impact students’ success.
- Schools Are Deploying Massive Digital Surveillance Systems. The Results Are Alarming. This piece in Education Week discusses the use and potential avenues for abuse of surveillance systems in schools.
- School Surveillance: The Consequences for Equity and Privacy. This publication by the National Association of State Boards of Education recommends key privacy principles in the context of surveillance technologies, including minimization, proportionality, transparency, openness, empowerment, equity, and training.
- Student Privacy in Massachusetts K-12 Schools. This report by the ACLU of Massachusetts outlines best practices and recommendations for Massachusetts public schools to balance technology use with student privacy.
- Student Activity Monitoring Software: Research Insights and Recommendations. The Center of Democracy & Technology (CDT) performed a survey of teachers, parents, and students about their experiences with, and attitudes toward, monitoring software.
- Online and Observed: Student Privacy Implications of School-Issued Devices and Student Activity Monitoring Software. CDT interviewed nine individuals from five local education agencies about how schools could address privacy concerns arising from the use of monitoring software.
- BluePrints for Healthy Youth Development. Provides a comprehensive registry of scientifically proven and scalable evidence-based interventions to promote youth development and health, including mental health. School and education leaders can refer to the BluePrints program search to find evidence-based and independently validated strategies for preventing student self-harm and improving student mental health.
- Children and the Internet: Laws Relating to Filtering, Blocking and Usage Policies in Schools and Libraries. This resource by the National Conference of State Legislatures gives a description of all the state laws that govern children’s use of the Internet.
- Fencing Out Knowledge. This report by the American Library Association details findings that schools and libraries nationwide are filtering out more of the Internet than what is necessary by law.
- Student Surveillance, Racial Inequalities, and Implicit Racial Bias. This journal article by Jason P. Nance discusses the implications of student surveillance on perpetuating racial inequalities in schools.
- Mixed Messages? The Limits of Automated Social Media Content Analysis. This report by the Center for Democracy and Technology discusses the limitations of social media analysis, with recommendations for policymakers on how to govern the use of these tools.
- Smart Investments for Safer Schools. This piece by the Center for American Progress outlines previous responses to bolster school safety and how certain initiatives, while well-intentioned, are not always in the best interest of students.
- SAMHSA’s Evidence-Based Practices Resource Center. The Substance Abuse and Mental Health Services Administration provides resources that schools may use to seek evidence-based strategies to address student mental health issues.
- Mixed Messages? The Limits of Automated Social Media Content Analysis. To understand the practical limitations of social media monitoring technology, schools and districts can consult the Center for Democracy & Technology report, which comprehensively examines the limitations of social media content analysis, lists questions to help organizations evaluate tools, and offers recommendations
- Healthy People 2020 Data. Having an adult that a youth or child can talk to is part of Healthy People 2020, which outlines the U.S. government’s national health goals.
- Best Practices for Serving LGBTQ Students. This report and toolkit by Learning for Justice provides best practices for educators to ensure that school policies support the mental health and well-being of LGBTQ students, and provides recommendations school leaders can follow to ensure use of a monitoring system does not inadvertently expose LGBTQ students to harm. Ensuring an inclusive and safe school climate for LGBTQ students helps reduce and prevent mental health challenges for this vulnerable group of students without relying on invasive monitoring.
- Developing Policy to Prevent Youth Suicide. This policy brief by the National Association of State Boards of Education provides guidance for education leaders developing model student suicide prevention policies.
 Compliance
Compliance Community Concerns
Community Concerns